SHA1: Secure Hash Algorithm 1
Salt: Randomly generated number, “the password of password”
hashcat: a free password recovery tool that comes with Kali Linux.
The latest time I saw SHA1 is with iPython. You can secure your IPython server by adding a password, where you can generate using the passwd() function and store that into your config file, more.
The generated hash is supposed to be in the format of `hash_algorithm:salt:passphrase_hash`. And we can see the salt is 12 characters long and the passphrase hash is 40 characters long.
Then I start thinking, can I use hashcat to recover my passcode if I forget the password? I first pass the hash code to hashid, which is an application that can give you a best guess which type of hash method the target is encrypted in. After I stripped off the salt, the hashid recognizes it should be SHA1, which is exactly the hash type how it was generated.
Then the next step is how to use hashcat to recover the code.
How hashcat works is you have to provision a list of passwords and a set of rules that hashcat need to follow, Then hashtag will leverage the computing power of GPU to quickly recover the password if the combo of initial list and rules will cover the target. To learn more about hashcat, here is a decent tutorial to get you started.
For the POC, I will just provide a list containing the password `datafireball` and use the straight attach mode.
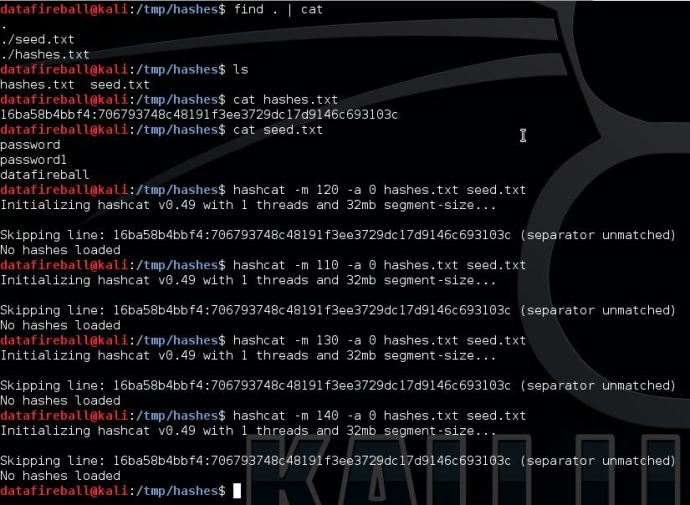
Based on the documentation about hashcat here, I think salt:pass should be matched to 120, or at least one of 110, 120, 130 and 140. However, neither of them works and they all prompted the error: separator unmatched.
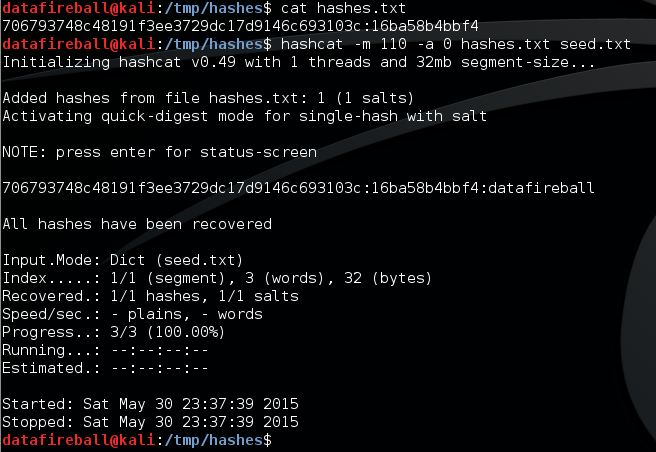
The interesting thing is after I switched the order of salt and phrase_hash, then the hashcat works using mode 110 (sha1($pass.$salt)).
Anyway, it is a fun time getting to know hashcat and sha1. Still need to figure out how the hashcode is generated using salt with password and looking forward knowing more about Kali Linux.