Control+K: delete all the characters after the cursor
Monthly Archives: September 2015
OPENSSL Public Key En/Decryption and Signature Verification
I took some notes here for quick reference.
openssl version
man openssl
# A pub/priv key
openssl genpkey _Algorithm RSA -pkeyopt rsa_keygen_bits:2048 -pkeyopt rsa_keygen_pubexp:3 -out privkey_A.pem
openssl pkey -in privkey_A.pem -out pubkey_A.pem -pubout
# B pub/priv key
openssl genpkey _Algorithm RSA -pkeyopt rsa_keygen_bits:2048 -pkeyopt rsa_keygen_pubexp:3 -out privkey_B.pem
openssl pkey -in privkey_B.pem -out pubkey_B.pem -pubout
# inspect
openssl pkey -in -text | less
# message.txt
echo ‘This is a test message sent from A to B’ > message.txt
# signature.bin
openssl dgst -sha1 -sign privkey_A.pem -out signature.bin message.txt
# ciphertext.bin
openssl pkeyutl -encrypt -in message.txt -pubin -inkey pubkey_B.pem -out ciphertext.bin
# decrypt
openssl pkeyutl -decrypt -in ciphertext.bin -inkey privkey_B.pem -out received-message.txt
# verify
openssl dgst -sha1 -verify pubkey_A.pem -signature signature.bin received-message.txt
Here is also a quick flow chart that I drew in Gliffy:

Here is a few take-aways from the plot:
(1) Private key is private, use to decrypt and should never share
(2) Public key is public, you can share it with anyone who is going to send you file and they gonna use it to decrypt
(3) The sender’s keys (pubic/private) are only used to verify the signature.
STUDY NOTES CRYPTOGRAPHY I – Statistical Tests
Statistical test on {0,1}^n:
an algorithm A such that A(x) outputs “0”(not random) or “1”(random)
A(x) = 1 if and only if the number of generated 1s are not hugely different from the number of 0s
A(x) = 1 if and only if the number of two consecutive 0s are not dramatically different from a quarter of the total number of bits.
A(x) = 1 if and only if max-run-of-o(x) <= 10 * log2(n)
Advantage[A,G] = | Pr[A(G(k))=1] – Pr[A(r)=1] |
Advantage close to 1 -> A can distinguish G from random
Advantage close to 0 -> A cannot distinguish, or the PRG is pretty much like random
secure PRG <=> Advantage[A,G] is negligible for all efficient statistical tests.
Thm(Yao’82), an unpredictable PRG is secure
STUDY NOTES CRYPTOGRAPHY I – Block Ciphers
Stream Ciphers, making OneTimePad practical by replacing random key by pseudorandom key.
At the second week, prof. Bonet talked about a few weak PRGs that are not recommended to be used in cryptography.
One is the linear congruential generator(LCG), and glibc randomizer. I also took a quick look a the built-in random number generator for python which uses Mersenne Twister as the core generator. Also, they mentioned “is completely unsuitable for cryptographic purposes”.
Negligible factor where epsilon is greater than 1/(2^30), likely happen over 1GB of data.
And when epsilon is smaller than 1/(2^80), then it won’t happen over life of key.
They the professor mentioned the convention later on in this course that factor will be negligible when it is exponential and non-negligible when it is polynomial.
Attack1: two time pad is insecure, when you use the same key to encrypt two messages, the eavesdropper capture the cipher, and simply run the xor of the cipher which turned out to be the xor of the messages with the PRG being removed!
Since English natural languages and ASCII contains enough redundancy for the hackers to infer the messages and separate them out based on the the XOR result. m1 xor m2 => m1, m2.
Project Venona is a real world mistake made by the Russians that reuse the same key, also Microsot PPTP and 802.11b WEP is also interesting stories to read.
FMS(Fluhrer, Martin and Shamir)0 attack is the stream cipher attach on that RC4 stream cipher.
Attack 2: no integrity – (OTP is malleable), if you have active attackers who actually manipulate the text and modify the message when it got decrypted.
CSS
Study Notes Cryptography I – Cryptography History
The first week of the course basically provides a brief introduction to Cryptography history and I have learned a few ancient cipher.
(1) Substitution Cipher
(2) Caesar Cipher (shift by 3)
(3) Vigenere Cipher (I implemented the encryption in Python and still need to implement the decrypt and cryptanalysis on natural languages to hack the password)
It is also interesting to learn the common ways to decrypt by using frequency of english letters, pairs of letters.
For single letter, the most frequent letters are “E”, “T”, “A”..etc and the most frequent diagrams are “TH”, “ER”, “ON”, “AN” – > “theRonan”.
And when the professor talks about the “mechanical age” of cryptography, it is really amazing to learn the existence of those rotor machines, including the famous Enigma Machine.
In the end, I finished the video which covers OTP (one time pad). It is good to learn Shannon’s research about the full secrecy around cryptography – Shannon Secrecy
I took a screenshot of the professor’s lecture:
Click to access 01.2-intro-annotated.pdf
Professor Dan Bonet shared two “magic cases” in cryptography on Coursera.
Privately Outsourcing Computation: like Google, search for encrypted data and returned encrypted result.
Verifiable Computing – Wikipedia
Zero knowledge (Proof of knowledge): prove you know without giving out the answer
Java Cipher getMaxAllowedKeyLength
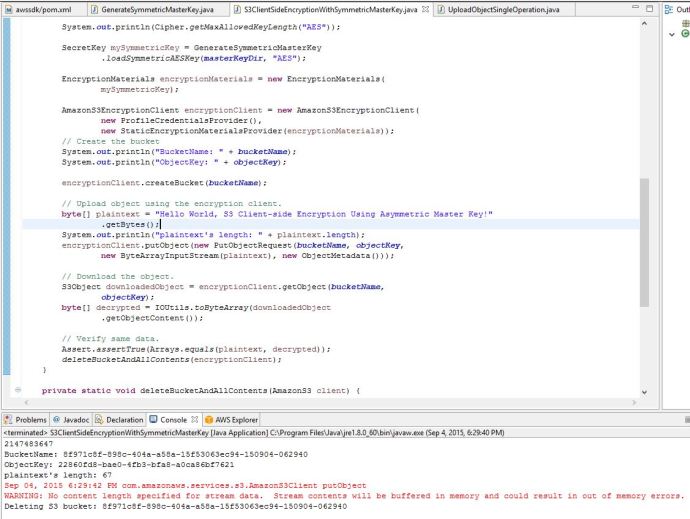
Today while learning how to encrypt data at client before loading to S3, I came across the javax.crypto package a lot.
Here is the sample code from AWS showing how to use symmetric key to encrypt data at client. However, after setting up the Eclipse plugin, Java SDK, I managed to generate the secret key file which is 32Bytes (256bit :)), however, when I run the second code, S3ClientSideEncryptionWithSymmetricMasterKey, it gave me errors around encryption – “Illegal key size or default parameters”. A quick google point me to Stackoverflow, of course.
I did a quick check of the key size limit on my machine by doing:
import javax.crypto.Cipher;
System.out.println(Cipher.getMaxAllowedKeyLength(“AES”));
And it showed only 128, which explains why it is unable to handle 256bit AES key, after following the JCE (Java Cryptography Extension) and copy the extension and policy files to the JRE->lib->Security folder, everything works now.
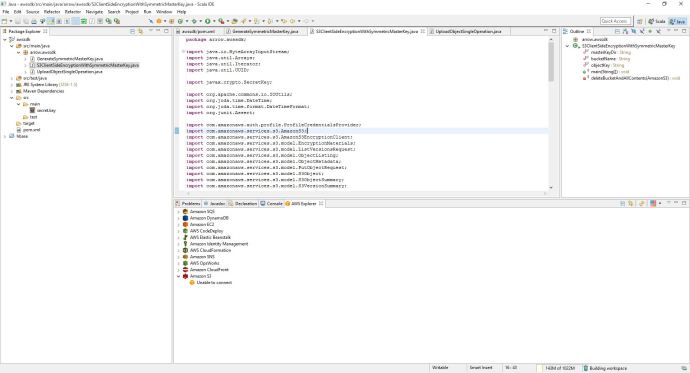
AWS SDK for Java
I have used BOTO which is the Python library to work with AWS, however, the AWS SDK for Java is more well developed and contains more features including the one that I care encyption on client.
Here is how I set up AWS SDK for Java on my brand new Windows 10 box 🙂
This is the screen shot of how the Eclipse plugin for AWS looks like, pretty handy to use.